Your personal information is valuable and that makes you a target for hackers. Access to your devices or your internet connections is also valuable for those intending to steal your money, commit online fraud or some other type of cybercrime. That’s why it’s important to understand how criminals operate and what you need to do to stay safe.
There are four main strategies that hackers use to gain access to your information, which are also highlighted in the table below for ease of reference.
Social Engineering
Social engineering is when the attacker uses the human psychology to generate a specific action or response. Hackers understand how people react to certain situations and can manipulate them into giving away sensitive information. Frequently, these social engineering attacks occur over the phone and leave victims feeling like they do not have time to consider their options. Remember that legitimate and respectable organisations will only contact you by phone if you have given them permission to do so. Moreover, the person contacting you should clearly identify themselves and take you through a client verification process, especially if it is an organisation like a bank that processes sensitive data. Finally, you should never feel as though you are being pressured into handing over information. If you feel uncomfortable about how an exchange is going, do not worry about simply ending the call. After all, it’s your data and keeping it safe is the most important thing to keep in mind in these circumstances.
Phishing and Smishing
Phishing is something many of us have heard of and it’s one of the hardest things to spot. In basic terms, phishing is when hackers impersonate a legitimate organisation, like a bank, and send an email or SMS asking individuals to urgently confirm sensitive information. The attack succeeds when the recipient clicks on a malicious link within the message.
Over time the quality of phishing attacks continues to improve and it can be difficult, at first, to differentiate between a legitimate message and one that isn’t. Here are some important things to keep in mind. Firstly, carefully check the actual email address or phone number that sent you the message. Have you received legitimate communications from these senders before? Also, is the message personalised. If it is something urgent, organisations will generally ensure that correspondence is addressed directly to you. Are you being asked to click on a link or open an attachment to proceed? This request is a red flag which you should not comply with. Hovering over a link should give you a preview of the web address you are being asked to click through to. This will help you to confirm the legitimacy or otherwise of the communication. At the end of the day, it’s better to be safe than sorry. If you have any doubts, delete the message and contact customer care through a safe channel you have used before so they can follow up if necessary.
Password guessing or brute force attacks
You are less likely to know that a password guessing or brute force attack is underway because in these types of attacks, there is no direct communication between you and the hackers. You may not realise it but there’s probably quite a lot of personal information about you out there on the internet. Birthdays, the town you live in, employment history, email addresses and phone numbers are probably all available in some way. With one item of information, hackers can then use software to attempt to access your accounts or devices by running combinations of the most often used passwords. That means that you should not use the town you were born in or where you live or your date of birth in your passwords and definitely do not use simply combinations like ‘1234’ or the current year just to make up the minimum character requirements. It is also important to change passwords frequently and to use a variety of characters to make these harder to guess. We all know that remembering different passwords is a hassle but you can always use a password manager to keep track.
Wi-Fi Security
The final ‘gateway’ that gives hackers access to your personal data and your devices is public Wi-Fi. Hackers are able to position themselves between you and a connection point in order to intercept your communications. To avoid this it’s important not to use public Wi-Fi to transfer important personal information or to make any online purchases. Instead, either use your mobile data connection or a secure home Wi-Fi connection (which doesn’t have an easy to guess password)
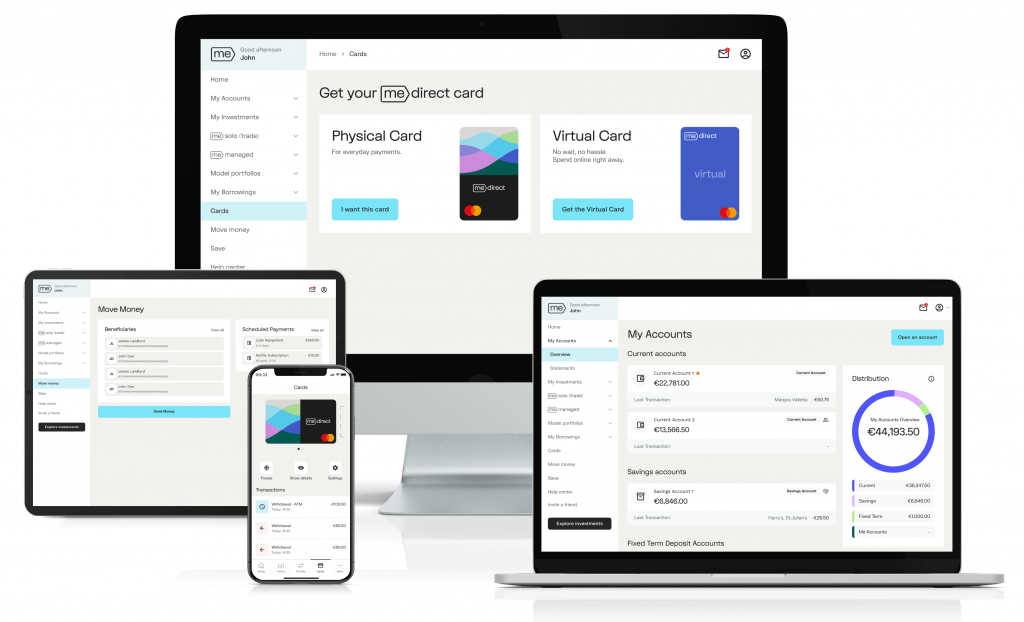
Cybercrime is a fact of life but there is a lot we call do to stay safe with vigilance being the most important factor. If you have any concerns regarding access to your MeDirect accounts, please call us on +356 2557 4400 or email customerservice@medirect.com.mt. If you believe that you have been hacked or are the victim of a cybercrime it is also important to contact the Cyber Crime Unit of the Malta Police on +356 22942231 or on email computer.crime@gov.mt
| Threat | How attackers operate | How to stay safe |
|---|---|---|
| Social Engineering | Attackers manipulate victims by pressuring them and taking advantage of their natural reactions. | If you are not sure stop the conversation and contact the person or organisation via a known safe method. |
Phishing and Smishing | Attackers design emails to impersonate legitimate sources and urging the victim to act quickly. The victim ends up clicking on a malicious link or providing sensitive data. | Stop, Look and Think! Verify URLs by hovering the cursor over links. If the URL does not match the link text or looks strange, it may be spoofed. Don’t click unless you are certain it is safe. |
| Password Guessing/ Brute-Force Attacks | Attackers tend to take advantage of short or easy to guess passwords such as those that include names, places, and dates | Make use of a password manager to create strong passwords. Do not share passwords and adopt different passwords for different accounts. |
| Wi-Fi Security | Cyber criminals take advantage of public Wi-Fi by positioning themselves between you and a connection point to intercept your information. | Do not use unsecure or public Wi-Fi networks to make online payments. Use mobile data or a secure Wi-Fi connection such as a home connection. |